The New Lateral Movement: Unpacking the Vercel Breach and the Hidden Risks of OAuth
In the world of cybersecurity, we often brace for the "big one"—the sophisticated zero-day exploit or the state-sponsored infiltration that bypasses every firewall we’ve spent millions to erect. But as the recent security incident involving Vercel reminds us, the most devastating supply chain attacks rarely start with a complex line of code. Sometimes, they start with a gaming cheat, a personal AI tool, and a single click on an "Allow All" button.
This isn’t just a report on a single company’s misfortune; it is a diagnostic of a systemic vulnerability in how we manage cloud permissions. As we navigate 2026, the lines between personal productivity and enterprise security have blurred to the point of invisibility. If you haven't audited your OAuth grants this quarter, you aren't just behind the curve—you might be the next headline.
The Stakes: Why Vercel Matters
For those outside the developer bubble, Vercel might not be a household name like Amazon or Google. However, in the tech ecosystem, they are a titan. Functioning as a frontend cloud platform, Vercel hosts the infrastructure for thousands of modern applications, particularly the "Neo-AI" startups that are currently defining the industry.
With rumors of an impending IPO, Vercel’s stability is a barometer for the health of the developer tools market. When Vercel is breached, it isn't just their internal data at risk; it's the secrets, environment variables, and infrastructure of the thousands of companies that rely on them.
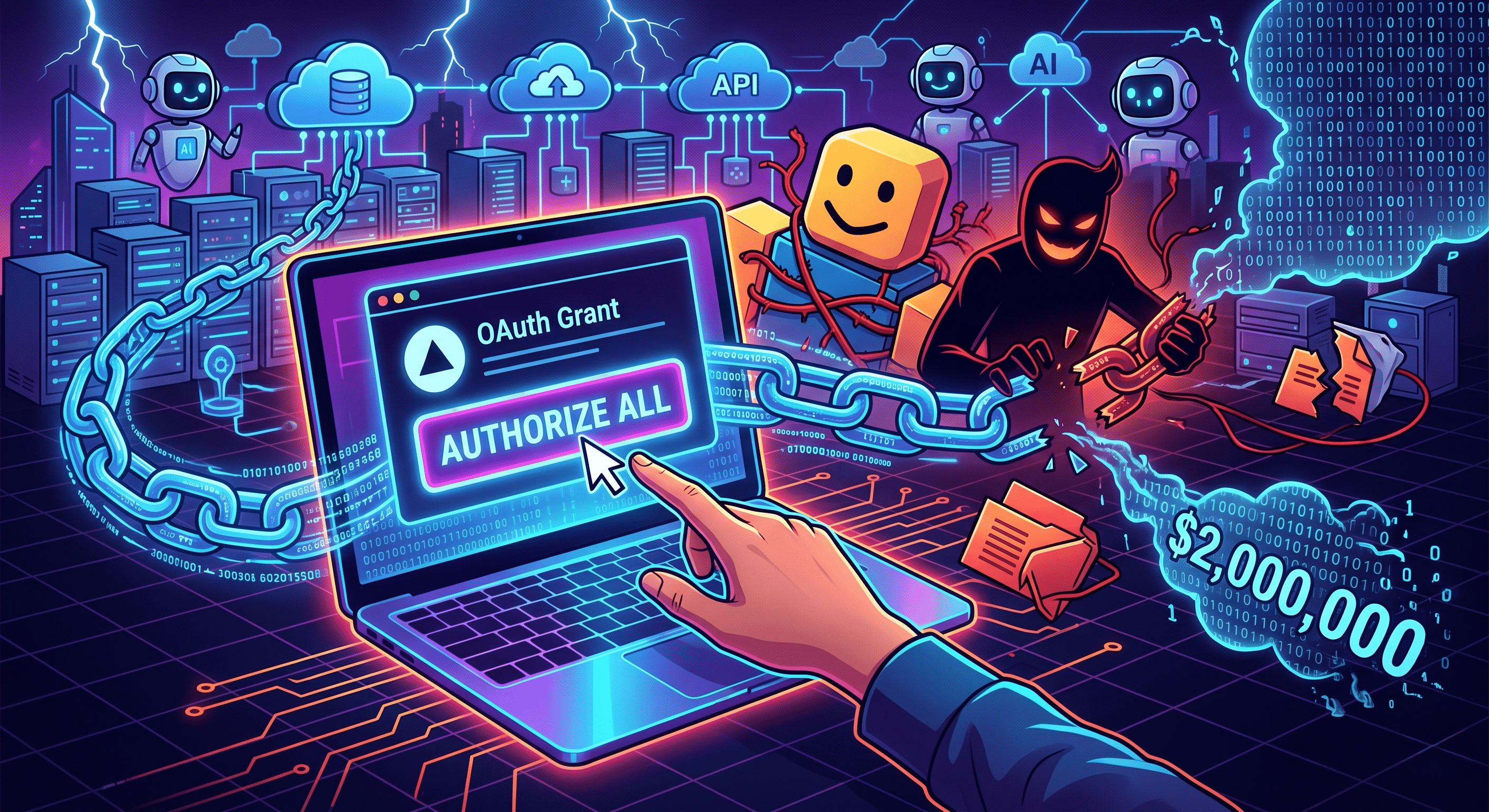
The Anatomy of a Breach: From Roblox to Revenue
The root cause of the Vercel breach is a masterclass in the "butterfly effect" of modern cybercrime. Thanks to insights from David Lindner (CISO at Contrast Security) and Jamie Blasco (CTO of Nudge Security), the sequence of events has been laid bare:
- The Initial Infection: It began at a third-party startup called Context AI. An employee there downloaded a Roblox Autofarm script—a classic gaming cheat. Embedded within that script was an "info-stealer" malware.
- The Credential Harvest: The malware did its job, harvesting credentials from the Context AI environment.
- The OAuth Pivot: Here is where the "shadow IT" element becomes critical. An employee at Vercel had signed up for Context AI as a personal user, but they used their Vercel enterprise account to do so. During the sign-up process, they granted the tool "Allow All" permissions via an OAuth token.
- The Sale: Because Context AI was compromised, the attackers gained access to that OAuth token. They then used that "trusted" connection to pivot into Vercel’s environment. This wasn't a zero-day exploit; it was an authorized door being opened by the wrong person.
Currently, reports indicate that threat actors are attempting to sell data related to this breach for upwards of $2 million.
Why MFA Failed to Stop the Bleeding
One of the most common misconceptions in management-level security is that Multi-Factor Authentication (MFA) is a silver bullet. In the case of OAuth-based attacks, that bullet is a blank.
As Jamie Blasco points out, OAuth essentially bypasses the traditional login flow once the initial grant is given. If an attacker steals an OAuth token, they don't need to know your password, and they don't need to intercept your SMS code. They are already "in" because the system sees them as a pre-approved integration.
Furthermore, if a grant has access to an employee’s email, attackers can initiate "forgot password" workflows for other platforms, effectively taking over accounts while bypassing MFA entirely. It is a terrifyingly efficient method of lateral movement.
The Rise of "Shadow AI" and Agentic Risks
We used to worry about Shadow IT—the department manager buying a SaaS subscription on a corporate credit card without telling IT. Today, we face Shadow AI.
Employees are eager to use "Agentic AI" tools to automate their workflows, summarize meetings, or clean up code. These platforms often sit at the center of a hub of OAuth grants with expansive scopes. Because many of these AI startups are young, they often lack the mature security programs required to protect the high-value tokens they are collecting from their users.
When a Vercel employee connects an unvetted AI tool to their corporate Google Workspace, they aren't just trying out a new feature; they are creating a permanent, high-privilege bridge into the heart of the enterprise.
Actionable Defense: Beyond Quarterly Audits
The "set it and forget it" mentality of permissions management is officially dead. To protect against the next Vercel-style breach, organizations must shift their strategy:
1. Implement Admin-Managed Consent
The most immediate fix is moving to a model of admin-managed consent. In Google Workspace and Microsoft 365, administrators can (and should) configure the environment so that employees cannot grant third-party apps access to enterprise data without a manual review. This single change would have blocked the Vercel employee from granting Context AI the enterprise-wide scope in the first place.
2. Continuous OAuth Inventory
OAuth grants accumulate like digital dust. Employees try a tool, forget about it, and eventually leave the company, but the grant remains active in the tenant. Organizations need continuous visibility—not just quarterly audits—into:
- Who granted the integration.
- The exact scopes granted (e.g., "Read-only" vs. "Full Access").
- Whether the integration has been used in the last 30 days.
3. Treat Tokens as High-Value Assets
The industry needs to stop viewing OAuth tokens as "convenience features" and start treating them as high-value credentials. Just as you wouldn't leave a master key under a doormat, you shouldn't allow over-permissioned tokens to exist for unsanctioned tools.
Final Thoughts: The Human Element
It is easy to blame the employee who downloaded a Roblox cheat, but the reality is that humans will always seek the path of least resistance—whether it’s to win a game or to be more productive at work.
The Vercel breach isn't a failure of one person; it's a reminder that our systems must be built to withstand human curiosity. OAuth is the new lateral movement. Until we treat it with the same level of scrutiny as our firewalls and encryption protocols, we are simply waiting for the next "trusted link" to break.
Security is no longer just about keeping the bad guys out; it’s about knowing exactly who—and what—you’ve already let in.


Comments
No comments yet. Be the first to share your thoughts!
Leave a Comment